Samba Active Directory with Bind9 on Separate Machines (Ubuntu 14.04)
We show how to install a Samba Active Directory over Bind9 DLZ on Ubuntu 14.04 with Bind9 and Samba PDC running on different machines.
| Bind9 Address | 10.0.0.5 |
| PDC Address | 10.0.0.10 |
In our case, the Samba PDC is a VirtualBox guest on the host running Bind9, sharing a VirtualBox folder (requires guest-additions), but the method would be very similar for two machines sharing a folder via NFS. While we have also succeeded in getting the NFS method to work, there lie many dragons along that route, not least of all security and identity mapping.
This document is a lead-sheet, not a recipe, and assumes the reader can install and provision a Samba Active Directory PDC over Bind9 DLZ. See
The PDC communicates zone information with Bind9 DLZ via files, which need to be shared. These files and directories are
| File or Directory | Bind9 Rights | Dynamic |
| /lib/samba/private/dns.keytab | read | yes |
| /lib/samba/private/named.conf | read | no |
| /lib/samba/private/dns/sam.ldb | read and write | yes |
| /lib/samba/private/dns/sam.ldb.d/ | read and write of members | yes |
The key is for the share to be located on the Bind9 box and remotely mounted on the PDC. Since the dns.keytab (and other) data is located on the Bind9 machine, DNS will continue working should the PDC go down.
Of course we do not want to share/expose the full /var/lib/samba/private of the PDC with Bind9, and so we replace the /var/lib/samba/private folders and files we need to share with links to the mounted share.
We encountered two dangerous curves.
- Bind9 DLZ expects to find these files in
/var/lib/samba/private. In this example we shall create such a directory on the Bind9 box and share it. Alternatively, create this folder and link to files and directories in some other shared folder (as we do on the PDC). - Bind9 requires write access to
/var/lib/samba/private/dns/sam.ldband all the files in/var/lib/samba/private/dns/. It would seem that this must also be the case when Bind9 and AD are on the same machine, although we have not tested that.
Install Bind9 and Share
Install Bind9 DLZ as a caching name-server, but make no other changes.
sudo apt-get install bind9 samba-libs
Make the directory that we are going to share with the PDC. This directory is going to contain those files and folders of the PDC /var/lib/samba/private directory that Bind9 DLZ needs access to. We do not share all these private files of course.
sudo mkdir /var/lib/samba/private
In our case, the virtual machine is run as a user virt-ad. So
sudo chown virt-ad:virt-ad /var/lib/samba/privatesudo chmod -R 770 /var/lib/samba/private
Put bind in the virt-ad group.
sudo usermod -a -G virt-ad bind
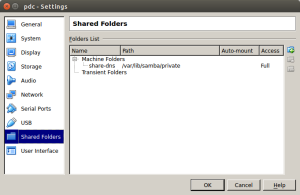
Share this folder with the virtual machine using name share-dns, say.
Do not choose to auto-mount. Auto-mounting did not work for us. We shall mount it ourselves.
Mounting the share on the PDC
Mount the folder being shared by the Bind9 box at /share-dns (say). In our case this is achieved by
sudo mkdir /share-dnssudo mount -t vboxsf share-dns /share-dns/
although the latter command needs to happen on start-up. For example, put mount -t vboxsf share-dns /share-dns/ in rc.local, or somewhere more sublime.
- Check that the share is indeed working, by touching files and one side and checking that they appear on the other, and vice versa.
- Notice that
root:rootfiles in the PDC share appear asvirt-ad:virt-adfiles in the Bind9 share, and hencebindhas group rights.
Installing and Provisioning the PDC
| Realm | MYDOMAIN.LOCAL |
| PDC Hostname | pdc |
With this model, the PDC is not a DNS server. So ensure a static address in /etc/network/interfaces, and edit /etc/resolvconf/resolv.conf.d/base
nameserver 10.0.0.5
domain mydomain.local
sudo apt-get install samba
sudo samba-tool domain provision --use-rfc2307 --interactive
with
| Realm | MYDOMAIN.LOCAL |
| Domain | MYDOMAIN |
| Server Role | dc |
| DNS backed | BIND9_DLZ |
Configuring the PDC to use the Bind9 server
sudo mv /var/lib/samba/private/dns.keytab /share-dns
sudo ln -s /share-dns/dns.keytab /var/lib/samba/private/dns.keytab
sudo mv /var/lib/samba/private/named.conf /share-dns
sudo ln -s /share-dns/named.conf /var/lib/samba/private/named.conf
sudo mv /var/lib/samba/private/dns /share-dns
sudo ln -s /share-dns/dns /var/lib/samba/private/dns
Check that these files reflect in /var/lib/samba/private on the Bind9 box.
- A security conscious installation may choose not to share
named.conf, and instead keep distinct copies on each side. Since Bind9 is facilitating the PDC, we probably do not want the PDC to be able to alternamed.conf. In fact, we suspect this file is not used on the PDC side.
sudoedit /etc/samba/smb.conf
allow dns updates = nonsecure and secure
dns forwarder = 10.0.0.5
# Thanks to Lars for this fix, it stops the syslog
# being spammed by the lack of a CUPS server.
printing = CUPS
printcap name = /dev/null
Configuring Bind9 DLZ
It remains to configure Bind9 on the DNS box. Because of the way we have named the folder that is shared, namely, /var/lib/samba/private, the following method is (almost) precisely that of Samba4 AD DC on Ubuntu 14.04
Following Samba4 AD DC on Ubuntu 14.04
sudoedit /etc/bind/named.conf.options
auth-nxdomain yes;
empty-zones-enable no;
// Adding this Samba generated file will allow for automatic DDNS updates
tkey-gssapi-keytab "/var/lib/samba/private/dns.keytab";
sudoedit /etc/bind/named.conf
Swap to the correct version of DLZ:
dlz "AD DNS Zone" {
# For BIND 9.8.0
# database "dlopen /usr/lib/x86_64-linux-gnu/samba/bind9/dlz_bind9.so";
# For BIND 9.9.0
database "dlopen /usr/lib/x86_64-linux-gnu/samba/bind9/dlz_bind9_9.so";
};
sudo nano /etc/bind/named.conf
Insert the following as the second include line:
include "/var/lib/samba/private/named.conf";
sudoedit /etc/apparmor.d/usr.sbin.named
Insert the following just before the final brace:
/usr/lib/x86_64-linux-gnu/ldb/** rwmk,
/usr/lib/x86_64-linux-gnu/samba/** rwmk,
/var/lib/samba/private/dns/** rwmk,
/var/lib/samba/private/named.conf r,
/var/lib/samba/private/dns.keytab r,
/var/tmp/* rw,
/dev/urandom rw,
A Dangerous Curve
Unfortunately that does not quite work. It seems Bind9 needs write access to /var/lib/samba/private/dns/sam.ldband all the files in /var/lib/samba/private/dns/
sudo chmod g+w /var/lib/samba/private/dns/sam.ldb
sudo chmod -R g+w /var/lib/samba/private/dns/sam.ldb.d/
Now we can restart Bind9 and all should work.
sudo service bind9 restart
Tail syslog to see that Bind9 started and loaded the AD zone.
Recent Comments